Hard skills are technical, measurable abilities such as risk assessment, threat analysis, and the implementation of security protocols that personnel security specialists must master.
Popular Personnel Security Specialist Resume Examples
Check out our top personnel security specialist resume examples that emphasize critical skills such as risk assessment, security protocols, and effective communication. These Resume Builder examples will help you showcase your qualifications to potential employers.
Ready to build your ideal resume? Use our Resume Builder for user-friendly templates specifically designed for security professionals, making it simple to create a professional document that stands out.
Recommended
Entry-level personnel security specialist resume
This entry-level resume for a Personnel Security Specialist effectively highlights the applicant's competencies in risk assessment and employee training, showcasing relevant experiences from previous roles. New professionals in this field must demonstrate their understanding of security protocols and crisis management skills to appeal to employers, even when they have limited work experience.
Mid-career personnel security specialist resume
This resume effectively showcases qualifications by highlighting achievements in compliance and risk reduction. The clear articulation of responsibilities and successes reflects the job seeker's readiness for advanced roles, demonstrating a strong progression in security expertise and leadership capabilities.
Experienced personnel security specialist resume
This resume demonstrates the applicant's extensive expertise as a personnel security specialist, highlighted by managing over 50 security clearances with a 20% process improvement. The clear formatting allows hiring managers to quickly recognize key achievements and skills relevant to the role.
Resume Template—Easy to Copy & Paste
Stephanie Butler
Portland, ME 04102
(555)555-5555
Stephanie.Butler@example.com
Professional Summary
Driven Personnel Security Specialist skilled in risk assessment, data protection, and threat mitigation. Proven track record of achieving 55% improvement in compliance and reducing incidents by 45%. Expertise in cybersecurity ensures robust protocols and safeguards.
Work History
Personnel Security Specialist
SecureTech Solutions - Portland, ME
January 2023 - November 2025
- Evaluated security risks, reducing incidents by 45%
- Managed sensitive data resources securely
- Implemented protocols for threat detection
Security Analyst
Fortress Guard Inc. - Portland, ME
January 2021 - December 2022
- Conducted audits, improving compliance by 55%
- Developed threat response plans in hours
- Reviewed threat intelligence reports monthly
Information Security Officer
ProtecSecure Systems - Portland, ME
January 2018 - December 2020
- Integrated new security tools, enhancing efficiency by 60%
- Monitored system vulnerabilities quarterly
- Trained staff on security best practices
Languages
- Spanish - Beginner (A1)
- French - Beginner (A1)
- Mandarin - Intermediate (B1)
Skills
- Risk Assessment
- Data Protection
- Threat Mitigation
- Security Audits
- Compliance Management
- Network Security
- Incident Response
- Vulnerability Analysis
Certifications
- Certified Information Systems Security Professional (CISSP) - International Information Systems Security Certification Consortium
- Certified Ethical Hacker (CEH) - EC-Council
Education
Master of Science Cybersecurity
Georgia State University Atlanta, Georgia
May 2017
Bachelor of Science Information Technology
University of Georgia Athens, Georgia
May 2015
How to Write a Personnel Security Specialist Resume Summary
Your resume summary is the first thing employers see, making it important to create a compelling introduction that highlights your fit for the role. As a personnel security specialist, you should emphasize your experience in risk assessment, compliance, and safeguarding sensitive information.
This profession demands showcasing skills related to security protocols, threat analysis, and strong communication abilities. It’s essential to present yourself as a reliable guardian of company assets and personnel.
To guide you in crafting an effective summary, we’ve included examples that illustrate what resonates with hiring managers:
I am a personnel security specialist with many years of experience in various security roles. I seek a position that allows me to use my skills and contribute to the safety of the organization. A company that values employee development and offers flexible working conditions would be perfect for me.
- Lacks specific achievements or qualifications related to personnel security, making it vague
- Emphasizes what the job seeker desires from their next role rather than highlighting their unique contributions
- Uses generic terms like "many years" without providing concrete examples or measurable results
Detail-oriented personnel security specialist with over 6 years of experience in risk assessment and compliance within corporate environments. Successfully decreased security incidents by 25% through the implementation of rigorous background screening processes and employee training programs. Proficient in threat analysis, access control systems, and regulatory frameworks, ensuring organizational adherence to security policies.
- Begins with a clear indication of experience level and area of expertise in personnel security
- Highlights quantifiable achievement that illustrates a significant impact on organizational safety
- Identifies specific technical skills and knowledge relevant to the role, improving credibility
Pro Tip
Showcasing Your Work Experience
The work experience section is important for your resume as a personnel security specialist, where you will showcase the majority of your skills and accomplishments. Good resume templates always emphasize this key area.
In this section, list your past jobs in reverse-chronological order. Each entry should include three to four bullet points that highlight your achievements and responsibilities in each role.
To clarify what makes an effective work history section, we’ll provide examples that illustrate both successful practices and common pitfalls:
Personnel Security Specialist
SecureTech Solutions – Atlanta, GA
- Conducted security assessments.
- Reviewed personnel files and documentation.
- Collaborated with law enforcement.
- Monitored compliance with security protocols.
- Lacks specific dates of employment
- Bullet points are too broad and do not highlight key achievements
- Emphasizes routine tasks rather than compelling contributions
Personnel Security Specialist
Global Security Solutions – Washington, DC
March 2020 - Current
- Conduct thorough background checks and security assessments for personnel, improving compliance rates by 30%.
- Develop and implement security training programs, improving staff awareness and reducing incidents by 20% over one year.
- Collaborate with law enforcement and internal teams to address security breaches, leading to a 15% decrease in potential threats.
- Uses powerful action verbs at the start of each bullet to highlight achievements clearly
- Includes specific metrics that demonstrate the applicant's impact on organizational security
- Showcases relevant skills such as collaboration and program development aligned with industry standards
While your resume summary and work experience are important, don't overlook the importance of other sections. Each part of your resume plays a role in showcasing your skills and qualifications. For more detailed guidance, refer to our complete guide on how to write a resume.
Top Skills to Include on Your Resume
A skills section is important for showcasing your expertise and making a strong first impression on employers. It quickly communicates your qualifications, helping you stand out in a competitive job market.
For a personnel security specialist, highlight technical skills such as risk management and familiarity with security systems like CCTV or access control software. These demonstrate your ability to protect organizational assets effectively.
Soft skills, including attention to detail, critical thinking, and effective communication, are interpersonal qualities that facilitate collaboration and ensure a safe environment for all stakeholders.
Selecting the right resume skills is important for standing out to employers. Many organizations use software to screen applicants, ensuring that only those with the essential skills make it through the initial selection process.
To effectively tailor your skills, carefully examine job postings for insights into what recruiters value most. This approach not only helps you align your qualifications with employer needs but also increases your chances of passing automated screening systems.
Pro Tip
10 skills that appear on successful personnel security specialist resumes
Improve your resume by highlighting sought-after skills that are essential for personnel security specialists. These competencies not only attract recruiters but also demonstrate your alignment with industry standards, as seen in our resume examples.
By the way, consider incorporating some of these key skills into your resume if they match your experience and the job's requirements:
Risk assessment
Attention to detail
Surveillance techniques
Conflict resolution
Interpersonal communication
Incident reporting
Emergency response planning
Data analysis
Regulatory compliance knowledge
Team collaboration
Based on analysis of 5,000+ safety security professional resumes from 2023-2024
Resume Format Examples
Selecting the ideal resume format is important for a personnel security specialist because it highlights your relevant skills, experience, and career advancement, ensuring you make a strong impression on potential employers.
Functional
Focuses on skills rather than previous jobs
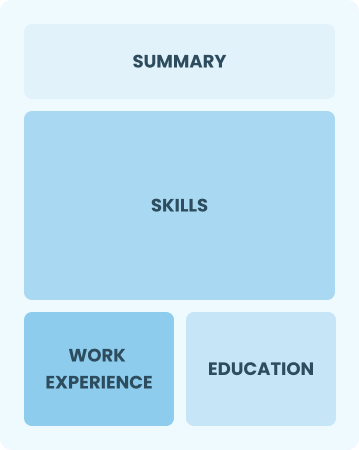
Best for:
Recent graduates and career changers with up to two years of experience
Combination
Balances skills and work history equally
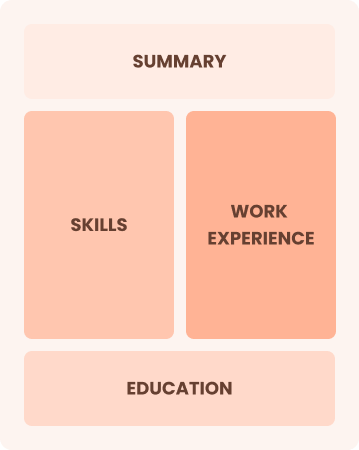
Best for:
Mid-career professionals eager to demonstrate their skills and pursue growth opportunities
Chronological
Emphasizes work history in reverse order

Best for:
Experts leading personnel security initiatives with extensive experience
Frequently Asked Questions
Should I include a cover letter with my personnel security specialist resume?
Absolutely. Including a cover letter can significantly improve your application by highlighting your qualifications and demonstrating your enthusiasm for the position. It gives you the chance to personalize your experience for recruiters. If you need assistance, consider visiting our guide on how to write a cover letter or use our Cover Letter Generator to make the process easier.
Can I use a resume if I’m applying internationally, or do I need a CV?
When applying for jobs abroad, use a CV instead of a resume as many countries favor this format for its detailed presentation of qualifications. To assist you, we offer resources that provide guidance on how to write a CV and effective CV formatting tailored to international standards. Additionally, exploring various CV examples can be beneficial in creating a compelling document.
What soft skills are important for personnel security specialists?
Soft skills like communication, problem-solving, and attention to detail are essential for personnel security specialists. These interpersonal skills foster trust with colleagues and ensure effective collaboration in maintaining safety and security protocols within an organization.
I’m transitioning from another field. How should I highlight my experience?
Highlight your transferable skills like communication, teamwork, and attention to detail from previous roles. These abilities show your capability and readiness for a personnel security specialist position. Provide concrete examples that connect your past successes to relevant duties in personnel security, showcasing how you can add value despite limited direct experience.
Where can I find inspiration for writing my cover letter as a personnel security specialist?
If you're on the hunt for personnel security specialist positions, check out our expertly crafted cover letter examples. These samples offer valuable insights into content ideas, formatting tips, and effective ways to showcase your skills and experiences. Let these resources guide you in creating standout application materials.
How do I add my resume to LinkedIn?
To increase your resume's visibility on LinkedIn, you should add your resume to LinkedIn directly or highlight key skills in the "About" and "Experience" sections. This approach helps relevant recruiters and hiring managers easily find qualified personnel security specialists, improving your chances of being discovered for new opportunities.