Hard skills such as data analysis, project management, and strategic planning are essential for senior consultants to drive successful business solutions and improve client outcomes.
Popular Senior Consultant Resume Examples
Check out our top senior consultant resume examples that emphasize critical skills such as strategic planning, project management, and client relations. These examples will guide you in showcasing your accomplishments to potential employers.
Ready to design your ideal resume? Our Resume Builder offers user-friendly templates specifically crafted for consultants, making it simple for you to create a professional presentation of your expertise.
Recommended
Entry-level senior consultant resume
This entry-level resume highlights the job seeker's strong analytical skills and proven track record in improving client revenue through strategic initiatives. New professionals in consulting must demonstrate quantifiable achievements and relevant skills to assure employers of their capability to contribute positively, even with limited experience.
Mid-career senior consultant resume
This resume showcases a well-rounded job seeker poised for senior roles, emphasizing achievements in efficiency and revenue growth. The strategic presentation of skills and accomplishments highlights their capacity for leadership in complex project environments, reflecting significant career advancement.
Experienced senior consultant resume
The work history section highlights the applicant's strong background as a Senior Consultant, showcasing significant achievements like a 35% increase in client satisfaction and $3M in cost savings. The bullet-point format improves readability, making it ideal for hiring managers seeking quick insights into accomplishments.
Resume Template—Easy to Copy & Paste
Chris Lee
San Diego, CA 92118
(555)555-5555
Chris.Lee@example.com
Skills
- Strategic Planning
- Business Analysis
- Process Improvement
- Project Management
- Client Relationship Management
- Data Analysis
- Leadership
- Operational Efficiency
Languages
- Spanish - Beginner (A1)
- French - Beginner (A1)
- German - Beginner (A1)
Professional Summary
Experienced Senior Consultant with 9 years in strategic planning, business analysis, and process improvement. Proven track record in enhancing operational efficiency and driving client satisfaction. Skilled in leadership, project management, and data-driven strategies.
Work History
Senior Consultant
Strategic Solutions Inc - San Diego, CA
January 2023 - March 2026
- Led a team of 5 consultants, increasing project efficiency by 25%
- Developed client-specific strategies, resulting in 1M revenue growth
- Implemented process improvements, reducing costs by 20%
Management Consultant
Innovative Consulting Group - Lakeside, CA
February 2020 - December 2022
- Analyzed business processes, improving workflow continuity by 30%
- Optimized client operations, resulting in a 15% cost savings
- Created comprehensive reports, enhancing decision-making efficiency
Consultant
Advanced Business Solutions - Lakeside, CA
January 2017 - January 2020
- Provided strategic advice, increasing client satisfaction by 20%
- Conducted market analysis, generating key insights for growth
- Facilitated workshops, enhancing employee skills and productivity
Certifications
- Certified Management Consultant (CMC) - Institute of Management Consultants USA
- Project Management Professional (PMP) - Project Management Institute
Education
Master of Business Administration Business Administration
Harvard University Cambridge, MA
June 2016
Bachelor of Science Economics
University of California, Berkeley Berkeley, CA
June 2014
How to Write a Senior Consultant Resume Summary
Your resume summary is the first opportunity to grab an employer's attention, making it important for setting the tone of your application. As a senior consultant, you should emphasize your strategic thinking, problem-solving abilities, and leadership experience to stand out in this competitive field. To guide you in crafting a compelling summary, we provide examples that illustrate effective approaches and common pitfalls to avoid:
As a senior consultant with many years of experience, I am eager to find a position where I can use my skills to help clients succeed. I'm looking for an organization that values teamwork and offers chances for advancement. I believe my background will be beneficial for the right team.
- Lacks specific details about the job seeker's expertise or notable achievements, making it vague
- Focuses more on personal desires rather than articulating what value the job seeker brings to potential employers
- Uses generic phrases that do not differentiate the job seeker from others in similar roles
Results-driven senior consultant with 8+ years of experience in strategic management and operational improvement across diverse industries. Achieved a 25% increase in client satisfaction scores through targeted process enhancements and training programs. Proficient in data analysis, stakeholder engagement, and project management methodologies, including Agile and Lean Six Sigma.
- Begins with specific experience duration and consulting expertise
- Highlights quantifiable achievement that reflects direct impact on client satisfaction
- Showcases relevant technical skills and management frameworks applicable to consulting roles
Pro Tip
Showcasing Your Work Experience
The work experience section is the centerpiece of your resume as a senior consultant, where you'll find the bulk of your content. Good resume templates always emphasize this section to highlight your professional journey.
Organize this area chronologically, listing your previous roles in reverse order. Use bullet points to detail specific achievements and contributions you made while in each position, showcasing your expertise.
To further clarify what makes an effective work history entry for a senior consultant, we will share some examples that illustrate best practices and common pitfalls:
Senior Consultant
Global Solutions Inc. – New York, NY
- Provided consulting services to clients.
- Attended meetings and discussed projects.
- Conducted research on industry trends.
- Assisted team members with tasks as needed.
- Lacks employment dates for context
- Bullet points are vague and do not highlight specific skills or achievements
- Focuses on basic responsibilities instead of showcasing strong contributions
Senior Consultant
Tech Innovations Inc. – San Francisco, CA
March 2021 - Present
- Lead cross-functional teams to deliver strategic solutions for clients, resulting in a 30% increase in operational efficiency.
- Analyze market trends and client data to develop customized strategies that improved customer satisfaction scores by 40%.
- Mentor junior consultants, improving their skills in project management and client engagement through hands-on training sessions.
- Starts each bullet with strong action verbs like 'Lead' and 'Analyze', showcasing the applicant's proactive approach
- Incorporates quantifiable results such as percentages to highlight achievements clearly
- Demonstrates relevant consulting skills like mentorship and strategy development, appealing directly to potential employers
While your resume summary and work experience are important components, don’t overlook the importance of other sections. Each part of your resume can highlight your skills and qualifications. For more detailed advice, be sure to check out our comprehensive guide on how to write a resume.
Top Skills to Include on Your Resume
Including a skills section on your resume is important for effectively showcasing your qualifications. This segment provides a snapshot of what you bring to the table, making it easier for both job seekers and employers to identify alignment with role expectations.
Hiring managers rely on this section to quickly gauge whether job seekers possess the necessary capabilities for success. Senior consultant professionals should highlight both their technical expertise and interpersonal skills, which will be discussed in detail below.
Soft skills, including leadership, communication, and adaptability, are important for senior consultants to build trust and drive successful project outcomes.
Selecting the right resume skills is important for aligning with employer expectations and passing automated screening systems. Many organizations use software to filter out job seekers lacking essential skills, so it's important to showcase your qualifications clearly.
To determine which skills to highlight, carefully review job postings for specific requirements. This approach not only helps capture the attention of recruiters but also ensures that your resume meets the criteria set by ATS.
Pro Tip
10 skills that appear on successful senior consultant resumes
Make your resume stand out to recruiters by showcasing high-demand skills for senior consultants. By the way, our resume examples highlight these and other essential qualifications, helping you apply with confidence.
Consider adding these 10 skills to your resume if they align with your experience and job requirements:
Strategic planning
Problem-solving
Leadership
Project management
Client relationship management
Analytical thinking
Negotiation skills
Change management
Business acumen
Communication
Based on analysis of 5,000+ business operations professional resumes from 2023-2024
Resume Format Examples
Selecting the appropriate resume format is important for showcasing your key skills, relevant experience, and career advancement. This ensures that potential employers quickly recognize your qualifications as a senior consultant.
Functional
Focuses on skills rather than previous jobs
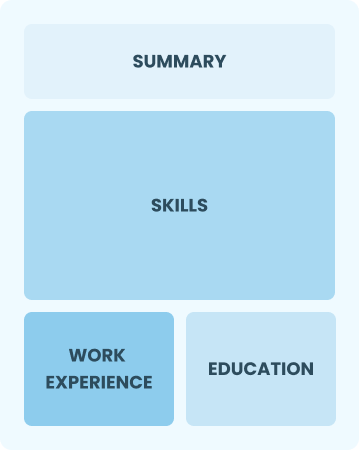
Best for:
Recent graduates and career changers with one to two years of experience
Combination
Balances skills and work history equally
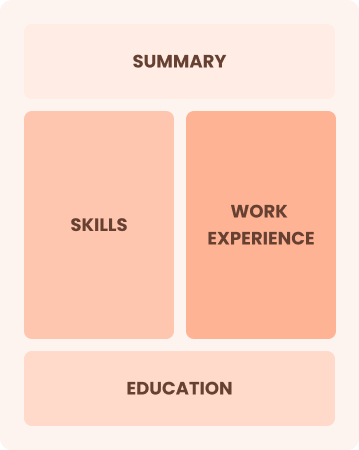
Best for:
Mid-career professionals focused on demonstrating skills and pursuing growth opportunities
Chronological
Emphasizes work history in reverse order

Best for:
Experienced professionals excelling in strategic leadership and specialized consulting
Frequently Asked Questions
Should I include a cover letter with my senior consultant resume?
Absolutely, including a cover letter is essential for making a strong impression on employers. A well-crafted cover letter can highlight your unique qualifications and show your enthusiasm for the position. If you need assistance, consider exploring our comprehensive guide on how to write a cover letter or use our Cover Letter Generator to streamline the process and create one effortlessly.
Can I use a resume if I’m applying internationally, or do I need a CV?
When applying for jobs outside the U.S., it's often best to use a CV instead of a resume. A CV provides a comprehensive overview of your academic and professional history. Check our resources for detailed CV examples and tips on how to write a CV that meets international standards.
What soft skills are important for senior consultants?
Soft skills like adaptability, problem-solving, and interpersonal skills are important for senior consultants. These abilities help you foster strong client relationships and collaborate well with teams, ensuring successful project outcomes and a positive work environment.
I’m transitioning from another field. How should I highlight my experience?
Highlight your transferable skills, such as strategic thinking, communication, and project management, which you developed in previous roles. These abilities demonstrate your potential impact in a senior consultant position even if you don't have direct experience. Provide concrete examples that connect your past successes to the demands of consulting, showing how you can contribute value to the team.
How should I format a cover letter for a senior consultant job?
To format a cover letter, start with your name and contact details. Follow this with a formal greeting and an engaging introduction that highlights your interest in the senior consultant position. Include a body paragraph summarizing your relevant experience, skills, and achievements. Finally, conclude with a powerful closing statement that encourages further discussion about your application.
How do I add my resume to LinkedIn?
To improve your professional visibility on LinkedIn, add your resume to LinkedIn by uploading it directly or summarizing key accomplishments in the "About" and "Experience" sections. This strategy not only showcases your qualifications but also helps recruiters and hiring managers easily discover you as a strong job seeker in your field.







