Hard skills are technical abilities like system design, cloud architecture, and programming languages that a solution architect must proficiently demonstrate.
Popular Solution Architect Resume Examples
Check out our top solution architect resume examples that emphasize key skills like system design, cloud computing, and project management. These examples will help you demonstrate your expertise effectively to potential employers.
Ready to build your ideal resume? Our Resume Builder offers user-friendly templates specifically designed for tech professionals, making your application process smoother and more efficient.
Recommended
Entry-level solution architect resume
This entry-level resume highlights the applicant's technical skills and accomplishments in optimizing cloud infrastructure and leading teams to improve deployment efficiency. New professionals in this field must convey their ability to apply theoretical knowledge practically and showcase any relevant projects or certifications to attract employer interest despite limited experience.
Mid-career solution architect resume
This resume effectively showcases key qualifications through quantifiable achievements and leadership roles. The structured presentation highlights the applicant's readiness for more complex challenges, demonstrating a strong trajectory in solution architecture and a commitment to innovation.
Experienced solution architect resume
This resume's work history section demonstrates the applicant's strong background as a solution architect, emphasizing their ability to optimize systems by 35% and reduce operating costs by $200,000 annually. The use of bullet points improves readability, making it easy for hiring managers to identify key achievements quickly.
Resume Template—Easy to Copy & Paste
Jane Kim
Hillcrest, NY 11510
(555)555-5555
Jane.Kim@example.com
Professional Summary
Solution Architect with 4 years of expertise in designing scalable cloud solutions, reducing system downtime and cost. Proficient in DevOps, Agile, and cloud architecture, enhancing team productivity and efficiency. Proven track record in optimizing software development processes and security protocols.
Work History
Solution Architect
Tech Innovations Inc - Hillcrest, NY
July 2023 - October 2025
- Architected scalable solutions saving 2M annually
- Led team to a 30% reduction in system downtime
- Implemented cloud strategies improving efficiency by 25%
Senior Software Engineer
Digital Solutions Group - Albany, NY
January 2021 - June 2023
- Developed software decreasing processing time by 50%
- Optimized codebase contributing to a 15% cost reduction
- Managed projects resulting in enhanced cybersecurity
Software Developer
Tech Visions Ltd - Hillcrest, NY
January 2020 - December 2020
- Implemented new features increasing user retention by 20%
- Collaborated on teams delivering projects 10% ahead of schedule
- Enhanced database security protocols reducing breaches
Languages
- Spanish - Beginner (A1)
- French - Intermediate (B1)
- German - Beginner (A1)
Skills
- Cloud Architecture
- Microservices
- DevOps
- Agile Methodologies
- Data Security
- System Integration
- Problem-solving
- Team Leadership
Certifications
- AWS Certified Solutions Architect - Amazon Web Services
- Microsoft Certified: Azure Solutions Architect Expert - Microsoft
- Certified Kubernetes Administrator - Cloud Native Computing Foundation
Education
Master's Degree Computer Science
University of Washington Seattle, Washington
June 2020
Bachelor's Degree Software Engineering
University of Texas Austin, Texas
June 2018
How to Write a Solution Architect Resume Summary
Your resume summary is the first opportunity to grab employers' attention, making it essential to create a lasting impression. As a solution architect, your summary should highlight your technical expertise and innovative problem-solving abilities.
Focus on showcasing your experience in designing scalable solutions and collaborating with cross-functional teams. This is your chance to present the effective projects that reflect your skill set.
To better understand how to craft an effective summary, let's look at some examples that illustrate what resonates with hiring managers and what pitfalls to avoid:
I am an experienced solution architect with a significant background in various technologies. I want a position where I can use my skills to advance in my career and help the company succeed. A role that offers flexibility and professional development opportunities would be perfect for me. I believe I can contribute positively if given the chance.
- Contains vague descriptions of skills without concrete examples or achievements
- Emphasizes personal desires over what the applicant brings to potential employers
- Uses generic language that fails to highlight specific expertise related to solution architecture
Results-driven solution architect with over 8 years of experience in designing and implementing scalable software solutions across various industries. Achieved a 30% reduction in system downtime by leading the migration to cloud-based infrastructure, improving application performance and user satisfaction. Proficient in microservices architecture, API development, and agile methodologies, collaborating effectively with cross-functional teams to deliver innovative technology solutions.
- Starts with specific years of experience and highlights a key area of expertise
- Contains quantifiable achievements that illustrate significant contributions to system performance
- Mentions relevant technical skills that are highly sought after in the field of solution architecture
Pro Tip
Showcasing Your Work Experience
The work experience section is the central component of your resume as a solution architect. This part of your resume is where you'll provide most of the content, and it's an essential feature in all good resume templates.
In this section, list your previous roles in reverse-chronological order with bullet points that highlight key achievements and projects you've worked on as a solution architect.
To help you refine this section, we will show examples demonstrating effective ways to present your work history. These examples will clarify what captures attention and what falls flat:
Solution Architect
Tech Innovations Inc. – San Francisco, CA
- Designed software solutions
- Collaborated with teams
- Managed project requirements
- Provided technical support when needed
- Lacks specific accomplishments or results from projects
- Vague descriptions fail to highlight unique skills or contributions
- Focuses on general duties instead of measurable impacts on business outcomes
Solution Architect
Tech Innovations Inc. – San Francisco, CA
March 2020 - Present
- Design and implement scalable cloud solutions for clients, resulting in a 40% reduction in operational costs over one year
- Lead cross-functional teams to deliver projects on time, achieving a customer satisfaction rate of 95% based on feedback surveys
- Conduct workshops to educate stakeholders on architectural best practices, improving team competencies and collaboration
- Uses powerful action verbs that clearly convey the job seeker's impact
- Incorporates quantifiable achievements to validate success and effectiveness
- Highlights relevant skills such as leadership and communication essential for a Solution Architect
While your resume summary and work experience are important components, don't overlook the importance of other sections that contribute to a well-rounded application. For additional insights on crafting an effective resume, be sure to explore our comprehensive guide on how to write a resume.
Top Skills to Include on Your Resume
A well-defined skills section is important for any resume as it allows you to quickly demonstrate your qualifications and make a strong impression on potential employers.
As a solution architect, focus on showcasing both hard skills and soft skills in your resume. Employers want candidate with the required industry skills as well as high-value interpersonal abilities.
Soft skills are interpersonal qualities such as problem-solving, collaboration, and effective communication that are essential for understanding client needs and delivering successful projects.
Choosing the correct resume skills is important for distinguishing yourself to potential employers. Numerous organizations employ automated systems that screen out applicants who do not possess the necessary qualifications for the position.
To tailor your skills effectively, thoroughly review job postings to gain insights into what recruiters are looking for. By emphasizing these key skills on your resume, you increase your chances of passing both human and automated review processes.
Pro Tip
10 skills that appear on successful solution architect resumes
Highlighting key skills in your resume can significantly increase your chances of catching a recruiter's eye for solution architect roles. You can see these pivotal skills illustrated in our resume examples, empowering you to approach job applications with confidence.
By the way, if you possess any of the following skills that align with your experience and the job requirements, consider adding them to your resume:
Cloud architecture
Problem-solving
Technical knowledge
Stakeholder management
Agile methodologies
System integration
Data modeling
Security protocols
Software development lifecycle (SDLC)
Collaboration tools
Based on analysis of 5,000+ computer software professional resumes from 2023-2024
Resume Format Examples
Choosing the right resume format is important for a solution architect because it highlights your technical expertise and project experience while effectively showing your career advancements.
Functional
Focuses on skills rather than previous jobs
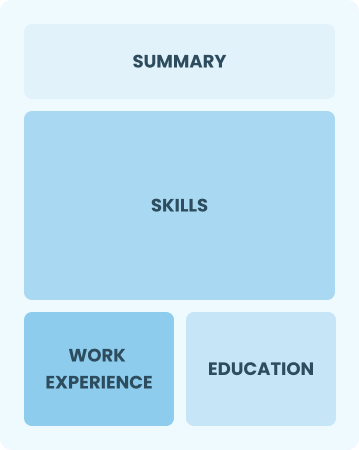
Best for:
Recent graduates and career changers with up to two years of experience
Combination
Balances skills and work history equally
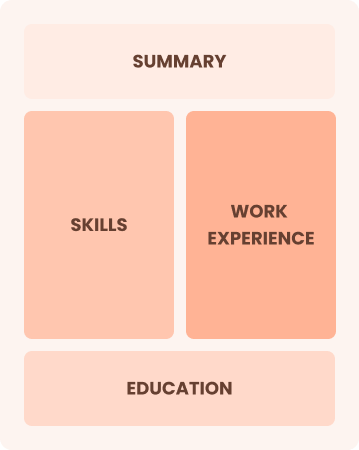
Best for:
Mid-career professionals focusing on their skills and future opportunities
Chronological
Emphasizes work history in reverse order

Best for:
Seasoned architects leading complex solutions and driving innovation
Frequently Asked Questions
Should I include a cover letter with my solution architect resume?
Absolutely, including a cover letter can significantly improve your application. It offers you the chance to showcase your personality and detail how your skills align with the job. To get started, explore our comprehensive guide on how to write a cover letter, or try our user-friendly Cover Letter Generator for quick assistance.
Can I use a resume if I’m applying internationally, or do I need a CV?
For international job applications, use a CV instead of a resume when the employer requests it or when applying in countries where CVs are standard. Explore CV examples and learn more about how to write a CV to create a professional document that meets global expectations.
What soft skills are important for solution architects?
Soft skills such as communication, collaboration, and problem-solving are essential for solution architects. These interpersonal skills enable effective teamwork and foster strong relationships with stakeholders, ensuring that technical solutions align with business needs and are delivered successfully.
I’m transitioning from another field. How should I highlight my experience?
When applying for solution architect roles, highlight your transferable skills like project management, communication, and analytical thinking. These abilities showcase your potential to thrive in the position even with limited direct experience. Use concrete examples from previous jobs to connect your accomplishments to the demands of architecture projects and client interactions.
How should I format a cover letter for a solution architect job?
To format a cover letter for solution architect positions, begin with your contact details and a formal greeting. Follow this with a compelling introduction that captures attention. Highlight your relevant skills and experiences in the body, ensuring each point aligns with the job requirements. Conclude with a strong closing statement that encourages further discussion about your application.
How do I write a resume with no experience?
If you’re aiming for a solution architect role but lack direct experience, check out this resume with no experience guide. Highlight relevant projects, coursework, and skills in systems design or software development. Showcase your problem-solving abilities and any internships or volunteer work that demonstrate your analytical thinking. Your passion for technology and willingness to learn can make a strong impression on employers.







